What Can Be Used to Increase the Strength of Hashed Passwords
Think your password is secure plenty?
You may desire to think again. In 2014, nearly half of Americans had their personal info exposed by hackers – and that doesn't fifty-fifty count the many companies that experienced breaches.
And with more and more businesses storing their information in the cloud and using SaaS solutions like business intelligence and hr software platforms, keeping your information safe becomes even more than important.
Selecting an obscure and complex countersign and changing it frequently can spell the deviation between keeping your data secure and having your personal information stolen. Nosotros've gathered insights and advice to empower you to tighten up your online security – and keep hackers out of your personal business organization.
To get started, we prepare out to discover merely how apace a seasoned cracker could "fauna-force" various types of passwords (systematically bank check combinations until finding the correct one) based on factors such as length and character types. We also created an interactive feature that lets you estimate how long it would take someone to crack a password at present compared with how long it took in the past. If you come upward with an idea for a potential password, our tester tin tell you only how secure it is. Just how many days, weeks, or years worth of security an extra letter of the alphabet or symbol make? How does password strength change over time? The answers just might surprise yous.
How stiff is a typical password at present – and how strong was it in the 1980s? Enter a word (non your electric current password) and drag the slider to select a year to find out how long it would take for someone to cleft the term if it were your countersign. It could accept anywhere from infinite time to a millennium to mere fractions of a millisecond.
You can turn the "give-and-take list" office on or off as you exam passwords. This tool works by cycling through a word list containing common words and passwords then evaluating other factors such as character types. If you lot enter a password not on the word list, the nifty time volition not be affected. Merely if your password is on the word list, information technology profoundly affects cracking time.
Note: The interactive tool is for educational purposes only. Although it does not collect or store your passwords, you should avoid using your current countersign.
How long should your password be?
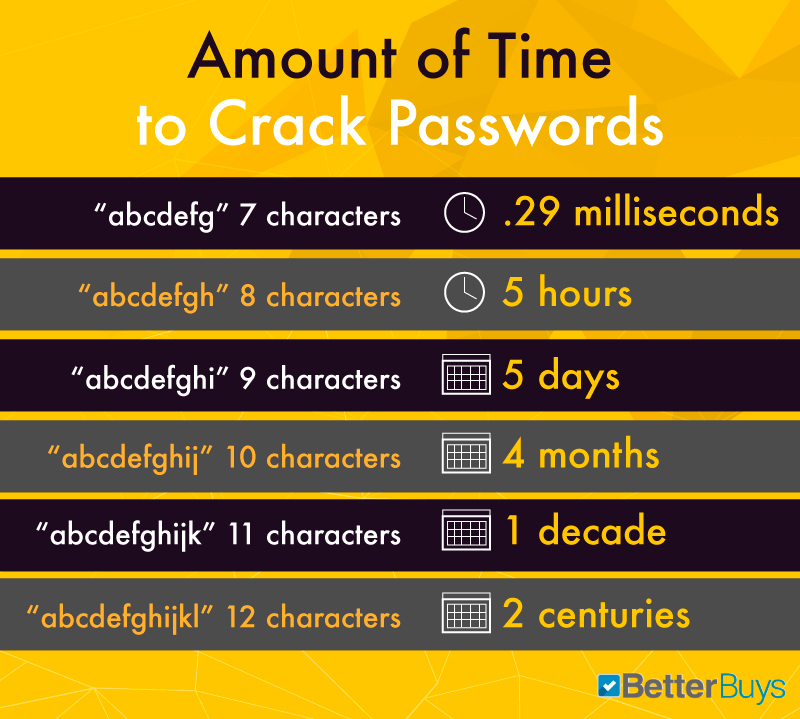
When it comes to passwords, 1 thing is certain: Size matters. Adding a single character to a password boosts its security exponentially. In a so-called "dictionary set on," a password cracker will utilize a word list of common passwords to discern the right one. The list above shows the difference that adding characters tin make when it comes to security.
For instance, if you take an extremely simple and mutual password that's 7 characters long ("abcdefg"), a pro could crack it in a fraction of a millisecond. Add merely one more than character ("abcdefgh") and that time increases to five hours. Nine-graphic symbol passwords take five days to interruption, 10-grapheme words take four months, and eleven-character passwords take 10 years. Brand it upwardly to 12 characters, and you're looking at 200 years' worth of security – not bad for one little letter.
alpha and numberic characters
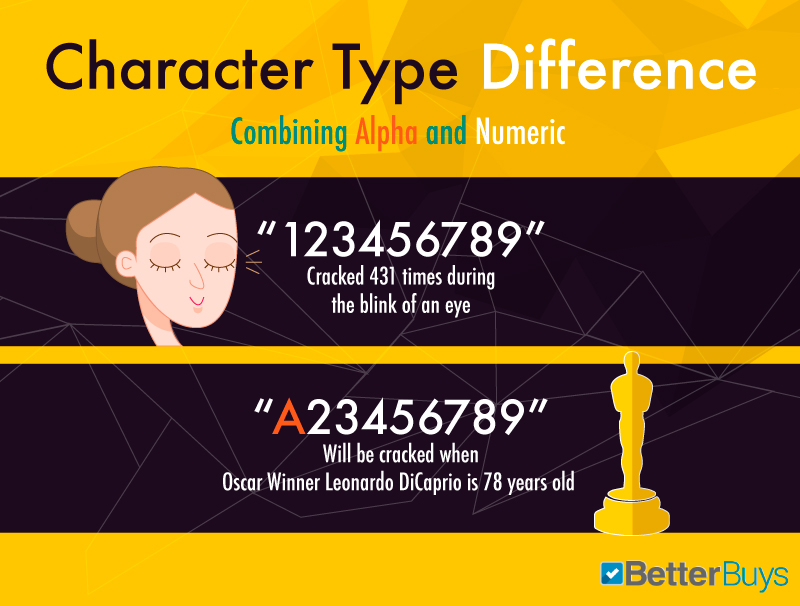
Combining numbers and letters rather than sticking with one type of character dramatically enhances countersign security. A string of nine letters or numbers takes milliseconds to crack. Add a single letter, and your countersign may go ambiguous enough to thwart password crackers for nigh iv decades.
However, it's non as simple as swapping your "e" for a "three" or adding a number at the end of a string of letters. Password attacking methods really have advantage of those common habits. Your all-time bet is to simply brand your countersign less predictable and more complicated.
asci, lowercase, and numeric characters

Combining several types of characters is an extremely effective way to brand your password more than cryptic. A simple, common word can be cracked in fractions of a millisecond. Inject a mix of lowercase and uppercase letters, numbers, and symbols (recollect @, %, and #), and your password can be secure for more than a decade.
password strength over time
.jpg)
Non every security result comes down to password graphic symbol types and length – time is also a major cistron. Over the years, passwords weaken dramatically every bit technologies evolve and hackers become increasingly skillful. For instance, a password that would take over three years to crack in 2000 takes just over a year to cleft by 2004. 5 years later, in 2009, the smashing time drops to four months. By 2016, the same password could be decoded in just over two months. This demonstrates the importance of changing passwords frequently.
what if y'all get hacked?
.jpg)
1 morning, you lot open your email, and everything has gone haywire: Friends are chatting you to say they've received spam from your address. Your login history looks odd. You have a pile of bounce-back messages in your inbox and a agglomeration of strange messages in your sent box. Yous've been hacked – and then what should you do?
First, recover your electronic mail account, and change your password (use our guidelines to formulate a strong 1). Complete all the steps, such equally changing security questions and setting up telephone notifications. Considering e-mail is filled with personal information, you lot should likewise notify your bank, PayPal, online stores, and whatsoever other accounts to discern whether a alienation has occurred. Be certain to alter other passwords too. Finally, notify your contacts in instance emails sent from your account accept compromised their information too. While non getting hacked at all is the best-case scenario, promptly taking these steps can make the best of a bad state of affairs.
Protect yourself
As time goes on, it only becomes more likely that your password will be hacked – putting your most personal information at risk. Past taking a few steps to enhance your password, you can exponentially minimize the risk of a breach. When it comes to passwords, size trumps all else – so choose ane that'south at least 16 characters. And exist sure to cull a mix of character types (numbers, uppercase and lowercase letters, and symbols) to farther enhance its security.
What else can you lot do? Steer articulate of words found in the dictionary, pronouns, usernames, and other predefined terms, every bit well equally commonly used passwords – the summit two in 2022 were "123456" and "password" (yes, you read that right). As well, never employ the aforementioned countersign in different places (that forgotten account at a site you never use could pb to a banking company business relationship breach). Consider using a password generator in order to become a complex countersign with no discernible pattern to assist thwart password crackers. Finally, if memorizing long strings of characters proves too taxing, consider adopting a password managing director that stores all your passwords. No password is perfect, but taking these steps tin can get a long way toward security and peace of heed.
Methodology
Using processor data collected from Intel and John the Ripper benchmarks, nosotros calculated keys per second (number of password keys attempted per second in a brute-forcefulness attack) of typical personal computers from 1982 to today.
The results from our interactive feature may differ from those of other online password-testing tools due to factors such as different equations, processors, and word lists.
Our data are based on the following equations:
Number of possible graphic symbol combinations:
(Password Type)^(Password Length)
Countersign Blazon is the number of possible characters.
Constructive Cores:
i/((1-Efficiency Constant)+(Efficiency Constant/Processor Cores)) The Efficiency Constant we used is 0.99, and we assume that 99% of the processor's operations can be defended to the password scissure.
Processor GFLOPS:
Processor Frequency * Effective Cores
Keys Per 2nd:
GFLOPS/Encryption Constant (gathered and calculated from John the Ripper benchmarks).
Time in seconds:
Seconds = Combinations/KeysPerSecond
Sources
- http://ark.intel.com/#@Processors
- http://openwall.info/wiki/john/benchmarks#John-the-Ripper-benchmarks
- https://www.d.umn.edu/~gshute/arch/functioning-equation.xhtml#instance
- https://www.pugetsystems.com/labs/articles/Estimating-CPU-Functioning-using-Amdahls-Constabulary-619/
- http://csrc.nist.gov/archive/pki-twg/y2003/presentations/twg-03-05.pdf
- http://money.cnn.com/2014/05/28/technology/security/hack-information-breach/
- http://gizmodo.com/the-25-nearly-popular-passwords-of-2015-were-all-such-id-1753591514
- http://world wide web.geekwire.com/2016/5-information-security-resolutions-yous-cant-afford-to-ignore/
- http://www.ucl.air conditioning.uk/media/library/blinking
- http://www.nps.gov/moru/faqs.htm
- http://lightning.nsstc.nasa.gov/primer/primer2.html
Fair Use
Experience gratis to share the images and interactive found on this page freely. When doing so, please aspect the authors by providing a link back to this folio and Meliorate Buys, so your readers can learn more about this projection and the related enquiry.
Source: https://www.betterbuys.com/estimating-password-cracking-times/
0 Response to "What Can Be Used to Increase the Strength of Hashed Passwords"
Post a Comment